You will need
- - Keylogger;
- - Punto Switcher;
- program for data recovery.
Instruction
1
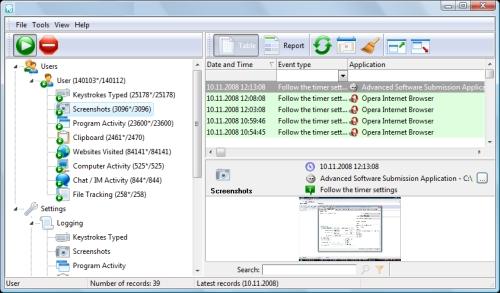
The easiest and surest way to find out everything that happens with your computer to install any Keylogger. This is a program that tracks all actions (including correspondence in all clients), and even takes screenshots at specified time intervals. For this you need to install the program on your computer. In the settings to set the required options to hide the user and password-protect (even if they learn the installation, delete or block can not). Most often, keyloggers are paid.
2
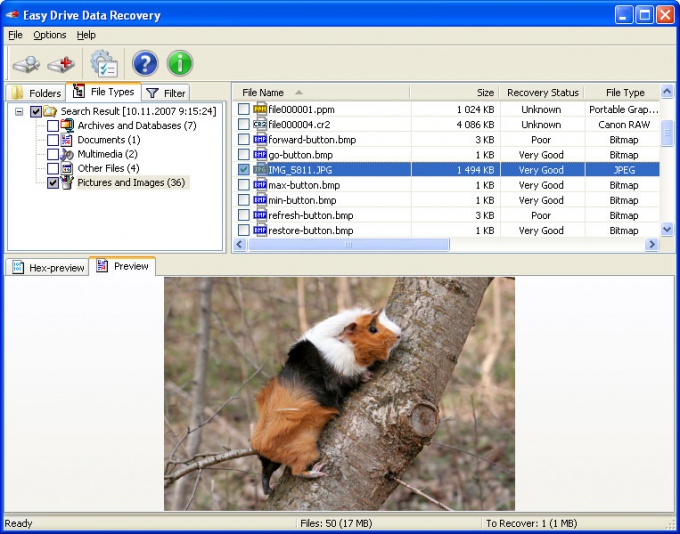
If you need to find the deleted history in your browser, then it can be done in the following way. Install one of the programs for data recovery - for example, DiscDigger, Recuva, Handy Recovery or Easy File Undelete, then run it and locate the file Places.sqlite. This will be the deleted browser history.
3
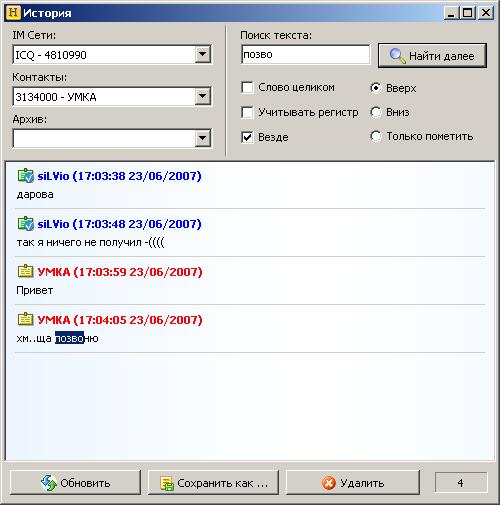
If you need to find out the history of correspondence in the various clients (ICQ, Qip, Skype, etc.), then find the folder of the desired program (usually it is in Program Files folder). It will have to find the History folder and to read the entire story. But this is possible only if the user does not remove it.
4
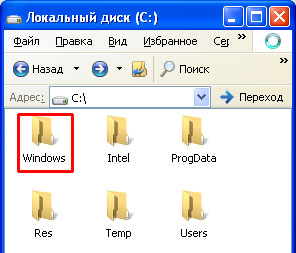
If you want to see what programs run on your computer, then it can be done very easily. Go to the C drive, click WINDOWS folder then Prefetch folder. Here shows the history of all open programs. Folder is not hidden.
5
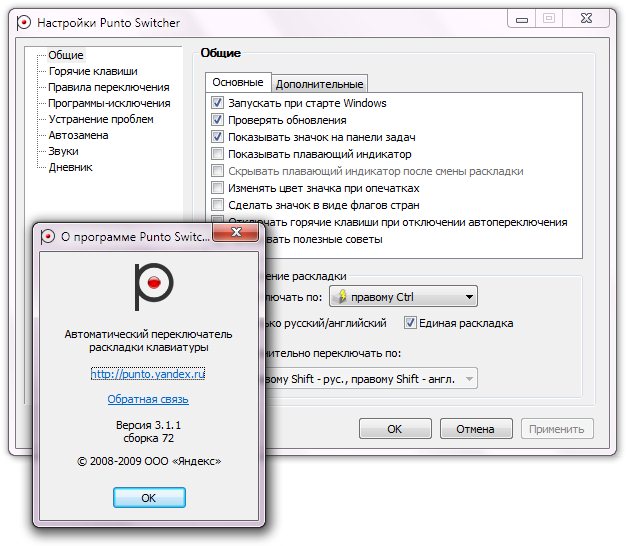
To view a history of all typed of printed characters on your computer, you can use Punto Switcher. This program automatically switches the keyboard layout from Russian to English depending on what the user writes. Still this program has a handy feature – keeping a journal. There are written all of the printed characters (in all programs). In the diary you can set a password, then view it can only you. Periodically it should be cleaned.
Note
If the user after the computer deletes all information with the help of specialized programs, to restore it would be almost impossible.
Useful advice
Do not restore the history on the computer if you are not able to work on the computer. This can lead to failures in the system.