Instruction
1
You need to run the command line cmd.exe. To do this, select the menu "start" "Execute"item.
2
In the window that opened, in line with a blinking cursor you need to dial cmd.exe. Press enter. Opened a standard window of the interpreter: this step can skip and go directly to the next step in the command prompt, your file Manager, for example FAR. 111111
3
Next you need to recruit a network team netstat.exe /?(you can just netstat /?). To run it you can press "Enter". The result is a list with prompts, and exactly what result can give the network program in the operation of certain keys. In this case we will be interested in more detailed information on active network ports and the specific application names.
4
Next you need to check scans as to whether the attacker is now our car. Enter the following command: Netstat -p tcp –n, or Netstat -p tcp –n. Here you want to draw your attention to the fact that do not occur very often one and the same external IP address (1st IP address of your local machine). In addition, about the attempted invasion may also reveal a huge number of records of this type are : SYN_SENT, TIME_WAIT with the same IP. Unsafe you can take frequent replays of network ports 139, 445 TCP and 137, and 445 UDP Protocol, with an external IP.
5
We can assume that we are lucky, external invasion is not seen, and we continue to look for "bad app" which devours the traffic.
6
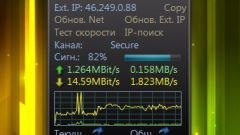
Entering the following: Netstat –b (here, admin rights required). It unloaded a huge Protocol operation statistics on the Internet your applications: This segment of the Protocol shows that the program uTorrent.exe (client to download and upload files in the BitTorrent network) produced the distribution of files on two machines in a network with open ports local 1459 and 1461.
7
Your right to decide whether to stop the application. Perhaps there is some sense to remove it from startup. There are already to detect the activity of other legitimate programs that work with online services: Skype, Miranda, and 2nd works via a secure Protocol https.
8
The ultimate goal of this analysis should be the identification of unfamiliar apps that without your knowledge, connect to the Internet (who knows what they convey). Then you have to use different ways of dealing with "bad" applications, starting with disabling them from startup to testing special tools.