You will need
- Configured and installed network connection.
Instruction
1
Algorithm determine the IPaddresses of the port varies depending on which devices and resources are being used at the moment. For the networked user computer that has access to certain resources, the algorithm is as follows:-Open a command prompt. To do this, click start, click Run, and using the keyboard, type cmd. This will bring up the window of the black command prompt window.-Enter in the command prompt window using the keyboard command rpccallserver, suitesare — the address of a resource on the Network. Click Enter to have the command executed. In the command prompt window opens a table with IPaddressesand their corresponding resources.
2
If the port used by a particular device, you will need to perform a number of simple steps to determine the IPaddress of this device:-Activate the device IP address of the port which you want to define. Open a command prompt with the above steps — click start, click Run, and keyboard keys, type cmd. Click Enter to have the command executed.-Enter via the keyboard in a command prompt window the command netstate, and click Enter to run. In the command prompt window will appear each activated coupling device and port identifiers in front of them.
3
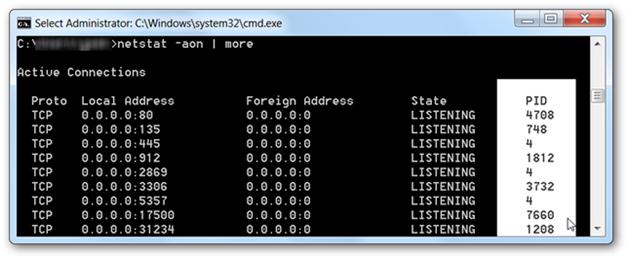
Instead of the last command you can also use the command NETSTAT-AON|MORE. This command will display to the right of the command prompt window will list the PID, process ID. In the illustration you can see that the PID of the device that has IP address 0.0.0.0:80, that is assigned to the eightieth port, will be equal to 4708.
4
Now the user can just load the task Manager — it is likely that you will need to use the "Show processes from each user, and the PID will be found in the list of applications can be used to determine which application manages the device with the specified IP.
5
Use information about IPaddresses, the interface can help to maintain anonymity and protect your operating system. To abandon its use impossible, because the IP is necessary for routing information. You can configure the connection of devices and applications via a proxy server that will receive and send data as if on his behalf. However, the vast majority of points in the service field x-forwarded-for address of the end user.
Useful advice
For privacy, you can also use special resources-anonymizers.