Instruction
1
The port may be closed as the modem / router and the provider side. In addition, it can be blocked by your firewall. Using standard Windows tools, you can check whether the closed port that the program uses for its operation.
In order to check open/closed ports in Windows, you must use the command line. To run press the key combination "Windows+R". After these steps, a window will open. It is necessary to enter "cmd". Then press "Enter".
In order to check open/closed ports in Windows, you must use the command line. To run press the key combination "Windows+R". After these steps, a window will open. It is necessary to enter "cmd". Then press "Enter".
2
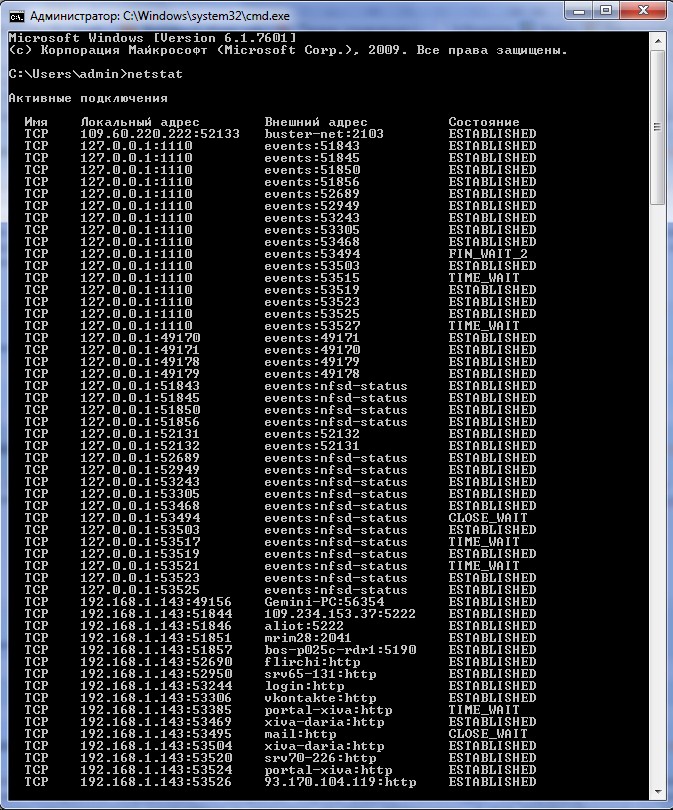
The screen will appear a black window, which experts call the Windows command prompt. You can now run the very tool that will allow you to view a list of closed ports. Enter in the command prompt "netstat".
3
After typing, press "Enter". In the command prompt window will display information about all the open ports on your computer. This will be followed by the domain name of your personal computer and are separated from it by a colon. Note that all portsthat are not specified in this list are private. And if a port that your app uses included in this list, it will be necessary to close the application is able to function normally.
Note
If the information provided isn't sufficient, you can explore all the possibilities of the utility "netstat", by running it with –h. This means that in command prompt you need to enter command "netstat -h". Then in the window that appears you will see help on the program "netstat".
Useful advice
Also there is a utility called "Windows Worms Doors Cleaner", which can not only show the open and closed TCP/UDP ports, but also to close the open port. Thus, you can further protect your computer from various online threats, as well as numerous viruses. The program "NetStat Agent 2.0" can replace the built-in "netstat".