You will need
- - computer with installed anti-virus software;
- - special tools for combating spyware.
Instruction
1
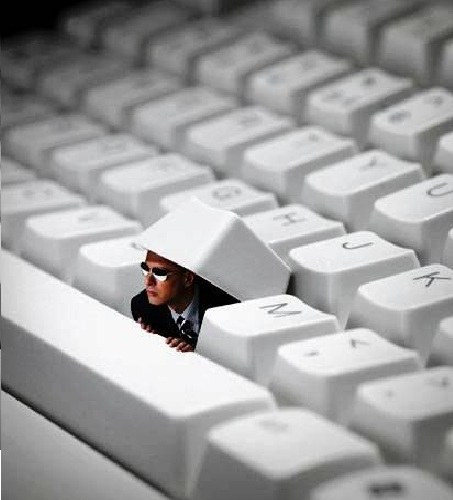
To check your computer for spyware, go to the Internet and download a special utility. This software in the Internet quite a lot, but you should listen to the opinions of other users and find out the reputation of the manufacturer of the program. Unfortunately, there are cases when under the guise of a special utility the user has voluntarily downloaded to your computer just the program-the spy. Fortunately, there are some signs that suggest that the computer has problems that need to be addressed urgently.
2
Run the browser program that is typically used for Internet access. Please note on the download page. If you are loading unknown page, which, moreover, still and you cannot change is a sure sign that the computer virus settled a class "hijacker". He usually changes the home page of the user to the page of the website from which the computer fall down all new and new portions of the virus troubles.
3
Observe the behavior of the operating system of the computer. If occasionally, it freezes or even crashing, you need to check the boot files and the activity of unknown processes at startup
4
Ask your provider or find out on their own, there is a sharp increase in Internet traffic. The presence of such a jump tells about the work of the source that is unknown, but it has the transmission and reception of large volumes of data.
5
Open task Manager, go to processes tab. Here with a probability of 80% to detect the activities of unauthorized programs. However, this can be done only by a specialist or experienced user. Particularly nasty spyware disguised as system processes, that is, looks quite peacefully. Moreover, the computer often refuses to remove malicious files, mistaking them for the service or system.