Instruction
1
That your computer is hacked or trying to hack, can indicate a variety of signs, and their detailed description you can find on the Internet. Consider a few options in the case if you notice signs of penetration on your computer.
2
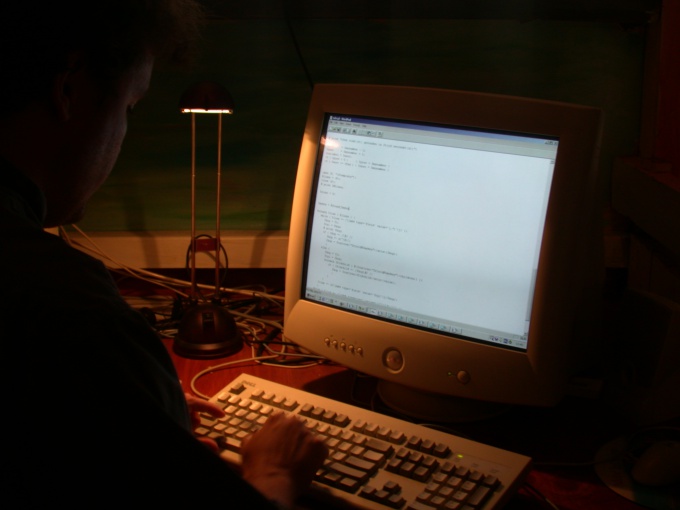
Open a command prompt, type the command "netstat –aon" (without the quotes). You will see a list of current connections. Suppose that you see an established connection on some port that does not use neither "legal" program. So, it is likely that your computer is the server part of backdoor Trojans that allows you to remotely control your computer.
3
On connection, it shows the line ESTABLISHED. In that case, if there is no connection and Trojan listening on a port waiting for a connection in the column "Status" will be LISTENING. When a connection is in the "External address" you will see the ip of the connected computer.
4
To receive information about this network address, use any of the appropriate network services. For example, this: http://www.all-nettools.com/toolbox/smart-whois.php.
5
Search for ip in the form field, click "Submit". If the received information indicates that the network address belongs to the address range (it is listed) such a provider, it is likely that you have managed to calculate the hacker.
6
But in most cases, in such a situation, you will be able to reach only to the proxy server at this break – the owners of the server are unlikely to give you information about who used their service. Although try to write a respectful letter stating the reason for the treatment.
7
Even if you managed to find the ip belonging to a specific person, it means nothing. It is possible that the user's computer is also compromised and is being used by a hacker as intermediates.
8
Possible situation in which the firewall reports that some present on your computer, the software tries to access the Internet. Chances are that your computer got a Trojan that collects sensitive data and sending them to a postal address.
9
In this case, you can try to explore the Trojan program to determine where exactly she sends her reports. For the study applies a set of tools: virtual machines, traffic analyzers, monitors, registry analyzers, PE files, and others. On the Internet you will find a detailed article on this topic.
10
One of the easiest ways to penetrate other people's computers is the use of the program Radmin. Many users, installing the program, forget to change the default password. A hacker scanning the network for open port 4899, finds similar computers and hacking into them with brute force.
11
If your computer was hacked through radmin, track the ip of the connected computer, then change the program password. Do not use old versions of this program, which is used to log on password only, they are the most vulnerable.
12
No matter how well was not protected your computer experienced hacker always has a chance to penetrate him. Therefore, never store in plaintext sensitive data, it is better to create an archive with these data and set a password. Do not use without firewall and antivirus. Using these simple rules, you will minimize the effects of infiltration on your computer.