Instruction
1
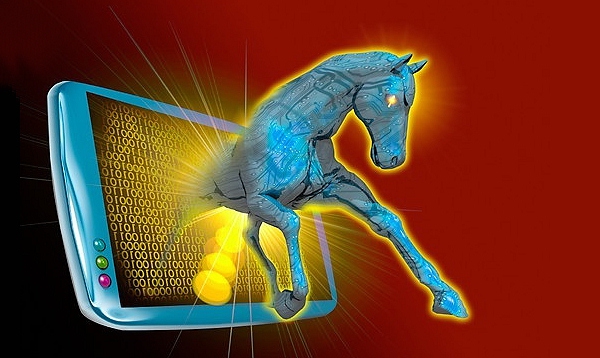
The Trojan horse was taken today to give a harmful virus which enters a computer disguised as a harmless and even useful software. The user downloads a program and does not even suspect that the code is written in its hostile function. When you run the program the Trojan is embedded in the computer system and starts creating all those outrages for which he was created by cyber criminals. The effects of infection by Trojans can be very different from unnerving, but it is harmless freezes, before the transfer of your data to fraudsters and causing you serious financial damage. Unlike a Trojan from a virus is that a Trojan is not capable of copying itself and then each of them was introduced into the system by the user. Antivirus programs are able to keep track of Trojan horses, but a special program handle it much better.
2
Moreover, almost all anti-virus vendors offer on their websites a free utility for catching Trojans. Eset NOD, Dr. Web, Kaspersky – any of these manufacturers can offer the freshest version of the program able to catch your uninvited guests. It is very important to use fresh utilities, the army of Trojans is updated daily with new, more cunning, and the day before yesterday ago the program may simply not recognize. Sometimes it makes sense to download a few programs, and run the system through them. In addition to tools produced by the antivirus companies, the network can find and antitroyanov from lesser-known manufacturers, but not less efficient in the search. For example AntiSpyWare, Ad-Aware, SpyBot and many others. If independent attempts of treatment of a computer does not bring the desired result, it is best to take the computer to a specialist who will be able to apply more serious measures.
3
But as you know, the best treatment is prevention. As mentioned above, Trojans are not materialists out of nowhere, users are downloading them to my computer. This can happen when downloading unknown files, clicks on suspicious links, opening file with unknown contents in the mail. Especially dangerous in terms of potential intrusion hacked program - this program at 99% will be infected with a Trojan virus, free lunch, alas, does not exist. So vigilance and caution, these two qualities will be more reliable than any antivirus. And a good antivirus, with a new database, regular inspection of special computer programs will close the last gap through which you could sneak a Trojan horse.