Instruction
1
Using modern terms, any encrypted message is the author who wrote it; the person to whom it is intended; and the interceptor — a cryptographer trying to read it.
2
Manual encryption there are two main methods — the replacement and relocation. The first is that the letters of the original message are replaced by others according to a specific rule. The second is that the letters, again according to the rule reversed. Of course, these two methods can be combined, which makes the cipher more resistant.
3
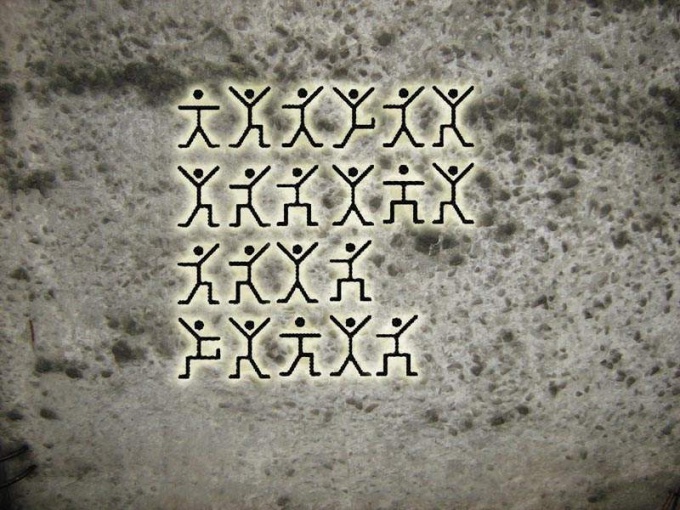
The simplest form of substitution cipher — cryptography. In this case the letters are changed to conditional icons: numbers, symbols, images, dancing men, and so on. To reveal the cryptographic message, it is enough to determine which symbol corresponds to which letter.
For this purpose, commonly used tables of frequency showing how often found one or the other letter in the language of the message. For example, in the Russian language on the first place in this table will be the letters "a", "e", "o". Substituting them instead of the most frequently occurring icons, you can decipher some of the words, and this, in turn, will give the values of other symbols.
For this purpose, commonly used tables of frequency showing how often found one or the other letter in the language of the message. For example, in the Russian language on the first place in this table will be the letters "a", "e", "o". Substituting them instead of the most frequently occurring icons, you can decipher some of the words, and this, in turn, will give the values of other symbols.
4
Stronger ciphers replace letters produced by key. For example, the key may become multivalued. To encrypt so the text over it many times to write a number key so that above each letter was a number. After that letter replaced by another, following after it in the alphabet through as many positions as specified by a number. The alphabet is a closed ring, that is, for example, the second letter after "I" will be "b".
5
Disclose that the cryptogram is more complicated, because for each letter of the cipher there are ten different interpretations. To decrypt we must first determine the key length and split the text into words. This is usually done using a table where the first line is the text to encrypt, and below it is the options where each letter of the cipher replaced a possible letter of the source text. Thus, in the table there are eleven lines.
6
Looking at what the options lead to the most natural division of the text into words, the cryptograph determines what letters are encoded spaces, and then finds one or more digits of the key. From this we can begin to draw conclusions, how many times the key is repeated in the text.
Substituting in place as yet unknown to letters options from the table, the cryptographer defines in which cases appear in the text of meaningful words and fragments.
Substituting in place as yet unknown to letters options from the table, the cryptographer defines in which cases appear in the text of meaningful words and fragments.
7
To facilitate the work of the cryptographer normally seeks to find any information about the content of the text or key. If you know what a signature is at the end of the document, or what word is there often to be repeated, then you can use this information to reveal part of the encryption key. Substituting the first occurrence in the document, the cryptographer finds the length of the key and learns some more parts of the original text.